Windows 365 as a Privileged Access Workstation
Windows 365 Cloud PCs are revolutionizing the way organizations secure privileged accounts. As cyber threats grow increasingly sophisticated, securing admin workstations is critical. Windows 365 offers a secure, manageable, and scalable approach to privileged access workstations (PAW), minimizing attack surfaces while ensuring productivity.
Why Windows 365 for Privileged Access?
Privileged Access Workstations (PAWs) are dedicated environments for admins, designed to reduce risk by isolating critical operations from daily workloads. Traditionally, PAWs required high maintenance and strict compliance. Windows 365 shifts this burden to a cloud-first model, providing:
- Isolation: Cloud PCs are separate from daily-use devices.
- Zero Trust Security: Enforced through strong authentication and conditional access.
- Centralized Management: Administered through Intune, reducing local attack vectors.
- Scalability: Instantly provisioned with a clean state when needed.
But to truly use Windows 365 as a PAW, security hardening is essential.
Hardening the Cloud PC Configuration
A default Cloud PC setup isn’t secure enough for privileged access. Strengthening security requires a multi-layered approach:
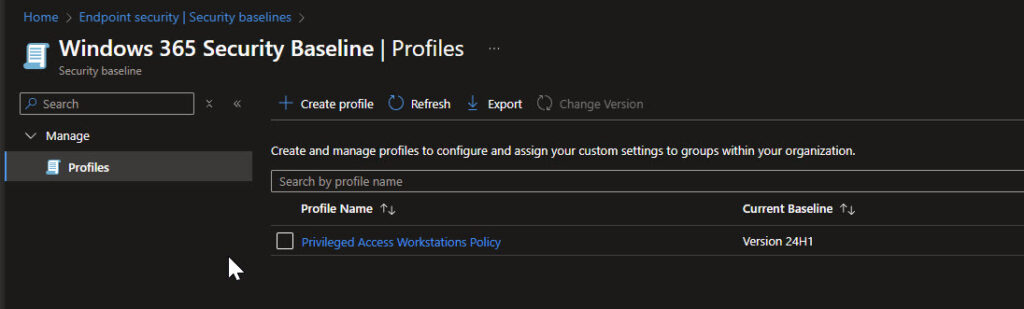
Security Baselines
Microsoft provides security baselines in Intune that enforce best-practice settings across devices. Apply the following:
- Windows 365 Security Baseline
- Microsoft Defender for Endpoint Baseline
- CIS or NCSC hardening guidelines for additional lockdown
Security baselines can be deployed via Intune > Endpoint Security > Security Baselines to enforce secure policies.
Defender for Endpoint (MDE) Integration
Microsoft Defender for Endpoint provides advanced attack detection and response capabilities. Ensure that your Cloud PC is fully onboarded to MDE:
- Enable Attack Surface Reduction (ASR) Rules to block untrusted scripts and macros.
- Configure Tamper Protection to prevent unauthorized changes.
- Leverage Endpoint Detection & Response (EDR) to monitor for suspicious activity.
URL Restriction (Proxy Configuration)
Cloud PCs should only access pre-approved URLs to prevent phishing and malicious downloads. While Intune can enforce URL restrictions, a more robust approach is configuring a manual proxy:
- In Intune, create a Device Configuration Profile > Device Restrictions.
- Configure a manual proxy server with the address 127.0.0.2:8080.
- Add Microsoft and admin URLs to proxy exceptions, ensuring necessary services remain accessible.
This setup prevents Cloud PCs from connecting to unapproved destinations.
Removing Admin Rights & Implementing Windows LAPS
Privileged access workstations should never be used with local admin rights. Enforce least privilege access:
- Remove users from local administrators group using Intune policies.
- Implement Windows Local Administrator Password Solution (LAPS):
- Enforces unique local admin passwords per device.
- Ensures credential rotation and encryption in Active Directory or Azure AD.
App Control for Business (WDAC & AppLocker)
One of the most effective ways to block malware is controlling application execution:
- Deploy App Control for Business via Endpoint Security > App Control for Business.
- Configure policies to allow only:
- Windows components
- Microsoft Store apps
- Intune-managed installers
- Trusted reputation applications
- Block all other software by default.
Firewall Hardening
Lock down network traffic to only essential services:
Inbound Traffic
- Block all connections except:
- Delivery Optimization (for patching)
- Remote Desktop (if needed for management)
Outbound Traffic
- Allow only critical network protocols:
- DNS, DHCP, NTP, NSCI, HTTP, and HTTPS
- Disable Local Policy Merge to prevent policy overrides.
- Enable Logging to track unauthorized connection attempts.
Securing Identity & Access
The strongest security control is identity protection. A Cloud PC is only as secure as the account signing into it.
- Enforce Strong Phishing Resistant MFA for all privileged accounts.
- Use Conditional Access to block access from non-compliant devices.
- Require Just-In-Time (JIT) access via Privileged Identity Management (PIM).
- Disable legacy authentication protocols (NTLM, Basic Auth).
Continuous Monitoring & Threat Detection
Even a fully hardened Cloud PC needs continuous security oversight.
Defender XDR & SIEM Integration
- Monitor Cloud PC activity with Microsoft Defender XDR.
- Forward logs to SIEM solutions (Microsoft Sentinel) for advanced threat hunting.
Automated Threat Response
- Set up automated remediation in Defender for Endpoint.
- Use Intune Compliance Policies to disable non-compliant Cloud PCs.
Is Windows 365 the Ultimate PAW?
Windows 365 offers a compelling alternative to traditional PAWs by delivering:
✅ Stronger isolation than hybrid PAW setups
✅ Easier management via Intune & MEM
✅ Consistent security posture across all admins
✅ On-demand provisioning for incident response
However, security is only as strong as its configuration. A Cloud PC must be hardened to function as a secure PAW. By implementing security baselines, identity protection, and network restrictions, organizations can minimize risk while maximizing flexibility.
